Media Summary: Today, the security of the world's digital infrastructure relies on traditional public-key based In this session, we present the OpenCrypto library that enables programmers to utilize all the capabilities of JavaCards (e.g., the ... Mansi Sheth, Security Researcher, Veracode Inc Are you overwhelmed by the overabundance of choices provided by the
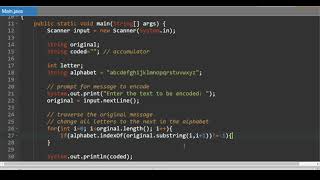
Hands On Cryptography With Java The Course Overview Packtpub Com - Detailed Analysis & Overview
Today, the security of the world's digital infrastructure relies on traditional public-key based In this session, we present the OpenCrypto library that enables programmers to utilize all the capabilities of JavaCards (e.g., the ... Mansi Sheth, Security Researcher, Veracode Inc Are you overwhelmed by the overabundance of choices provided by the