Media Summary: Hightouch's new homepage makes identifying and resolving Learn about current threats: IBM Security Guardium: To enhance service security and accountability, the speakers have developed a comprehensive reporting system that scores ...
Feature Release Protecting Data Driven Operations At Scale - Detailed Analysis & Overview
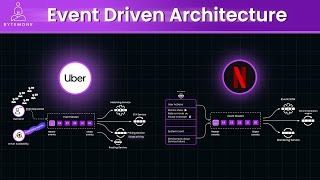
Hightouch's new homepage makes identifying and resolving Learn about current threats: IBM Security Guardium: To enhance service security and accountability, the speakers have developed a comprehensive reporting system that scores ... Learn how Rejuvenation, part of Williams-Sonoma, Inc., is using AI agents to handle product copy at In this talk, Joshua will present a modular, scalable system for streaming anomaly detection for enterprise cyber security, along ... AI cybersecurity → The power of AI Security → Check out ...