Media Summary: As AI evolves from summarization to independent action, the As autonomous agents operate 24/7, static logins are no longer enough to Ready to become a certified SOC Analyst - QRadar SIEM V7.5 Plus CompTIA Cybersecurity Analyst? Register now and use code ...
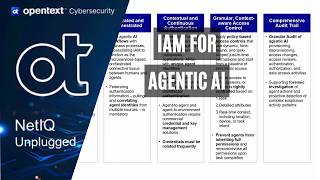
Extending Identity Security For The Agentic Enterprise - Detailed Analysis & Overview
As AI evolves from summarization to independent action, the As autonomous agents operate 24/7, static logins are no longer enough to Ready to become a certified SOC Analyst - QRadar SIEM V7.5 Plus CompTIA Cybersecurity Analyst? Register now and use code ... Watch Yinon Costica demonstrate how Wiz secures AI and cloud applications by using the Wiz Red Agent to act as a friendly ... Ready to become a certified watsonx Generative AI Engineer - Associate? Register now and use code IBMTechYT20 for 20% off ... Ready to become a certified z/OS v3.x Administrator? Register now and use code IBMTechYT20 for 20% off of your exam ...
AI agents should not execute sensitive actions without runtime authorization backed by cryptographic proof. In this demo, our ... AI agents are not just another workload—they are autonomous actors operating across systems, data, and workflows. That breaks ... In this deep-dive technical session from ROCon 2025, Mayuresh Ektare, Vice President of Product Management for Matt White (Global CTO of AI at the Linux Foundation, CTO of the