Media Summary: Pentester Academy is the world's leading online cyber security education platform. We offer: 2000+ training lab exercises ... This lecture is part of my undergraduate security course at the University of Cambridge. 00:00 Challenges and intro 01:40 What is ... Sign in for free and try our labs at: Pentester Academy is the world's leading online ...
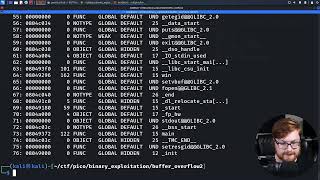
Exploit Research Buffer Overflow File Read - Detailed Analysis & Overview
Pentester Academy is the world's leading online cyber security education platform. We offer: 2000+ training lab exercises ... This lecture is part of my undergraduate security course at the University of Cambridge. 00:00 Challenges and intro 01:40 What is ... Sign in for free and try our labs at: Pentester Academy is the world's leading online ... Making yourself the all-powerful "Root" super-user on a computer using a PS, jump into the HackTheBox Cyber Apocalypse CTF! Help the channel grow with a ... This tutorial goes over the basic technique of how to
48.Buffer Overflow Attack on a Web Application Help the channel grow with a Like, Comment, & Subscribe! ❤️ Support ➡ ↔