Media Summary: Hello hackers today we're going to be talking about In this video, I have demonstrated how we can chain up Help the channel grow with a Like, Comment, & Subscribe! ❤️ Support ➡ ↔
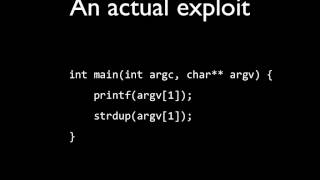
Exploit Development Format Strings Series 1 6 Intro And Dumping Sensitive Data - Detailed Analysis & Overview
Hello hackers today we're going to be talking about In this video, I have demonstrated how we can chain up Help the channel grow with a Like, Comment, & Subscribe! ❤️ Support ➡ ↔ 7th video from the "Practical Buffer Overflow Exploitation" course covering the basics of Binary Exploitation. In this video we'll look ... Disclaimer This is educational purpose video only. I did not harm anyone I just do ctfs and make that walkthrough and explain ... Hi guys this is Alex and I'm going to give a brief