Media Summary: Telegram group : contact me on Gmail at shraavyareddy810.com contact me on ... Hii there from Codegency! We are a team of young software developers and IT geeks who are always looking for challenges and ... In the paper, information passes across the network by means of various paths. It is essential to provide security for the information ...
Encryption And Decryption Using Blow Fish Algorithm 1 Crore Projects - Detailed Analysis & Overview
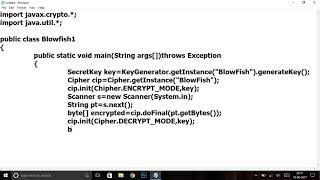
Telegram group : contact me on Gmail at shraavyareddy810.com contact me on ... Hii there from Codegency! We are a team of young software developers and IT geeks who are always looking for challenges and ... In the paper, information passes across the network by means of various paths. It is essential to provide security for the information ... In this video you will learn the theory related to It was very disappointing looking up tutorials for encryping passwords and seeing md5 hashing and AES. AT LEAST ADD A ... 18BCE1355 - Ananya Sajwan CSE3501 - Information Security Analysis and Audit - Digital Assignment 3 This video describes the ...
This Chanel for Education perpose, basically for Programmer. Check out our website: Follow Telusko on Twitter: Follow on Facebook: ...