Media Summary: Video Topic: DNS penetration testing involves assessing the security of Domain Name System (DNS) services to identify ... 1. How to simulate an IoT device with web service? 2. How to setup two LANs connected with a router and protected with firewall? Hi everyone, This video is a demonstration of conducting a successful
Dns Attack Lab - Detailed Analysis & Overview
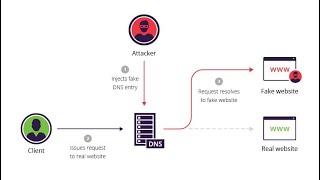
Video Topic: DNS penetration testing involves assessing the security of Domain Name System (DNS) services to identify ... 1. How to simulate an IoT device with web service? 2. How to setup two LANs connected with a router and protected with firewall? Hi everyone, This video is a demonstration of conducting a successful CYSE 330: Introduction to Network Security Students: Tyvelt Singleton & Dania Castro Macbook Desktop VM IPs: User VM ... In this video, we delve into the world of Ever typed a website address and ended up somewhere unexpected? That's the power of