Media Summary: 5 Digital Asset Security Risks [Complete Video: 39 minutes] About ACCESS US 2026 ACCESS 2026 — Halborn's Premier From social engineering to supply chain attacks, the threat landscape is rapidly evolving. Learn how
Digital Asset Security Salesforce - Detailed Analysis & Overview
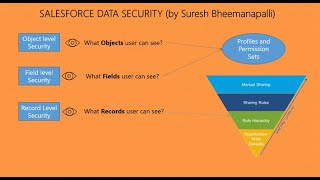
5 Digital Asset Security Risks [Complete Video: 39 minutes] About ACCESS US 2026 ACCESS 2026 — Halborn's Premier From social engineering to supply chain attacks, the threat landscape is rapidly evolving. Learn how This is an installation and setup walkthrough video for our In this episode, we explore the Trusted IP vs Log-In IP Ranges, Log In Hours, Profiles, and Permission Sets. Understanding these ... Granting users too much data access can leave your business exposed. The best defense? The Principle of Least Privilege.



![5 Digital Asset Security Risks [Complete Video: 39 minutes]](https://i.ytimg.com/vi/bu3KpLEgVMs/mqdefault.jpg)