Media Summary: Gate Smashers Shorts: Watch quick concepts & short videos here: Subscribe ... To get better at system design, subscribe to our weekly newsletter: Checkout our bestselling System Design ...
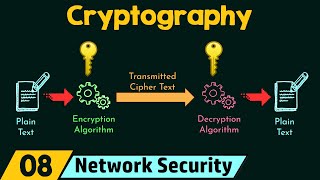
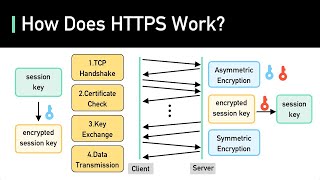
Day 4 Cryptography Explained Encryption Pki Protocols - Detailed Analysis & Overview
Gate Smashers Shorts: Watch quick concepts & short videos here: Subscribe ... To get better at system design, subscribe to our weekly newsletter: Checkout our bestselling System Design ...