Media Summary: TLS in Kubernetes MASTERCLASS A complete, in-depth walkthrough of To get better at system design, subscribe to our weekly newsletter: Certified Kubernetes Security Specialist (CKS) preparation! !!! USE Ubuntu 24.04 instances instead of the 20.04 shown in the ...
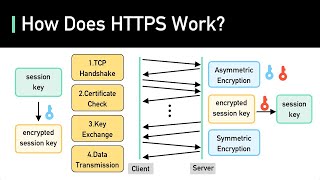
Day 30 How Https Ssh Work What Is Encryption Symmetric Asymmetric Encryption Cka 2025 - Detailed Analysis & Overview
TLS in Kubernetes MASTERCLASS A complete, in-depth walkthrough of To get better at system design, subscribe to our weekly newsletter: Certified Kubernetes Security Specialist (CKS) preparation! !!! USE Ubuntu 24.04 instances instead of the 20.04 shown in the ... Welcome to Kubernetes Class 3 where you can achieve 25+ LPA In this class, we cover production-style Kubernetes setup ...