Media Summary: Security+ Training Course Index: Professor Messer's Course Notes: ... Cyber Security operations dashboard at Dubai Export city COP28 CNBC's "Power Lunch" team is joined by John Carlin, former assistant attorney general for the U.S. Department of Justice's ...
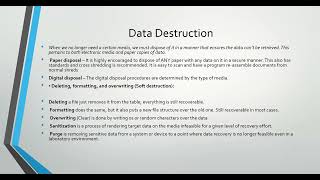
Cybersecurity Demystifying Data Destruction - Detailed Analysis & Overview
Security+ Training Course Index: Professor Messer's Course Notes: ... Cyber Security operations dashboard at Dubai Export city COP28 CNBC's "Power Lunch" team is joined by John Carlin, former assistant attorney general for the U.S. Department of Justice's ... Are you prepared to embark on a life-changing journey exploring With the advances in distributed computing, machine learning techniques, and Big Tough, realistic CISSP Practice Tests designed to expose gaps before exam day. Don't go in unprepared.** Challenging ...
IBM Security QRadar EDR : IBM Security X-Force Threat Intelligence Index 2023: Welcome To Hackworld - Your Go-To For Hacker Stories Credits: Shawn Ryan Show This video is for transformative ... Looking for a Job? I Give You the 5 Best Ways to Find a Job in Cyber: I know many of you are struggling. I see your posts. I talk to ... Subscribe to see more videos like this in the future →