Media Summary: Hi guys we will learn in this tutorial series about the basics of In this video, we dive into the fascinating world of Let me know if you wanna see this implemented into a login system. This video shows how to use MessageDigest to create a very ...
Cryptography In Java 3 1 Hashing - Detailed Analysis & Overview
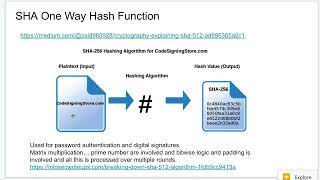
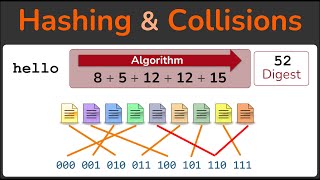
Hi guys we will learn in this tutorial series about the basics of In this video, we dive into the fascinating world of Let me know if you wanna see this implemented into a login system. This video shows how to use MessageDigest to create a very ... This video is from the vault of Spring Framework section of the course. Check out the course links below. Check out our courses: ... Link for playlists: Link for our website: ... Today, the security of the world's digital infrastructure relies on traditional public-key based