Media Summary: Michigan - Applied Generative AI Specialization ... Gate Smashers Shorts: Watch quick concepts & short videos here: Subscribe ... Today we're going to talk about how to keep information secret, and this isn't a new goal. From as early as Julius Caesar's Caesar ...
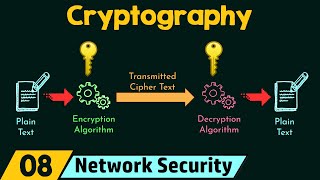
Cryptography Basics Encryption And Decryption - Detailed Analysis & Overview
Michigan - Applied Generative AI Specialization ... Gate Smashers Shorts: Watch quick concepts & short videos here: Subscribe ... Today we're going to talk about how to keep information secret, and this isn't a new goal. From as early as Julius Caesar's Caesar ... Intellipaat Cyber Security Training Courses: In this ... Mia Epner, who works on security for a US national intelligence agency, explains how