Media Summary: Gregor Leander, Mohamed Ahmed Abdelraheem, Hoda AlKhzaimi, and Erik Zenner Technical University of Denmark, Lyngby, ... The Vigenere cipher, dating from the 1500's, was still used during the US civil war. We introduce the cipher and explain a ... This is a video companion to my slide attack tutorial. The tutorial itself can be found here: ...
Cryptanalysis Of Printcipher - Detailed Analysis & Overview
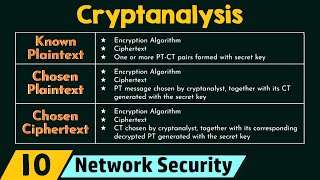
Gregor Leander, Mohamed Ahmed Abdelraheem, Hoda AlKhzaimi, and Erik Zenner Technical University of Denmark, Lyngby, ... The Vigenere cipher, dating from the 1500's, was still used during the US civil war. We introduce the cipher and explain a ... This is a video companion to my slide attack tutorial. The tutorial itself can be found here: ... But more ordered more ordered agree more higher degree The Vigenère Cipher was invented in the 16th century to encrypt secret texts. It was long regarded as a secure method and ... Link for playlists: Link for our website: ...
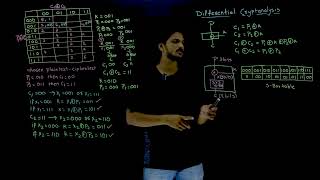
cyber security unit -1 full handwritten notes btech cse student kurukshetra university . .Telegram channel ... Subhadeep Banik Cryptanalysis of the Full Spritz Stream Cipher This is a video of my talk at the LayerOne 2013 security conference. In it, I discuss the basics of differential Talk at crypto 2012. Authors: Mohamed Ahmed Abdelraheem, Martin Ågren, Peter Beelen, Gregor Leander. Talk by Dr. Somitra Sanadhya, IIIT Delhi in the workshop on Trustworthy Computations in Mobile and Cloud Environments at NIIT ...