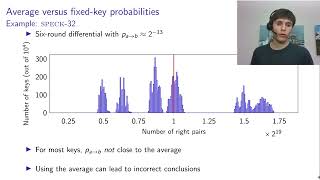
Media Summary: Paper by Tim Beyne, Vincent Rijmen presented at Crypto 2022 See Link for playlists: Link for our website: ... Cryptography and Network Security by Prof. D. Mukhopadhyay, Department of Computer Science and Engineering, IIT Kharagpur.
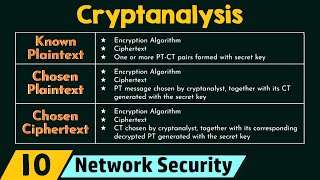
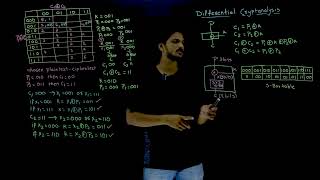
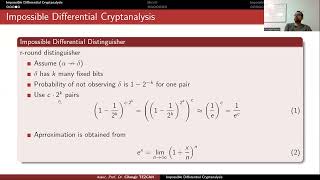
Cryptanalysis L6 Differential Cryptanalysis - Detailed Analysis & Overview
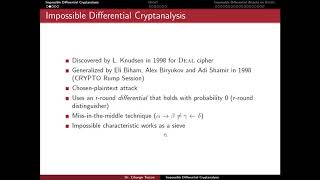
Paper by Tim Beyne, Vincent Rijmen presented at Crypto 2022 See Link for playlists: Link for our website: ... Cryptography and Network Security by Prof. D. Mukhopadhyay, Department of Computer Science and Engineering, IIT Kharagpur. Traveling? Find the best deals on flights & hotels ▸ ⚡ Up to 70 % off electronics on Amazon ... cyber security unit -1 full handwritten notes btech cse student kurukshetra university . .Telegram channel ... 4 - Related-Tweak Impossible Differential Cryptanalysis of Reduced-Round TweAES
Complete playlist: Applied Cryptography ... Paper by Christoph Dobraunig, Yann Rotella, Jan Schoone presented at FSE 2020 See ...