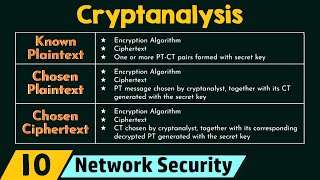
Media Summary: Lars Schlieper, Ph.D. Student, Ruhr-University Bochum Marloes Venema, Ph.D. Student , Radboud University Chao Niu, Ph.D. Attack types, time complexity, memory complexity, data complexity, total break, global deduction, local deduction, distinguisher, ... The Vigenere cipher, dating from the 1500's, was still used during the US civil war. We introduce the cipher and explain a ...
Cryptanalysis I - Detailed Analysis & Overview
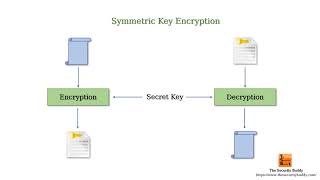
Lars Schlieper, Ph.D. Student, Ruhr-University Bochum Marloes Venema, Ph.D. Student , Radboud University Chao Niu, Ph.D. Attack types, time complexity, memory complexity, data complexity, total break, global deduction, local deduction, distinguisher, ... The Vigenere cipher, dating from the 1500's, was still used during the US civil war. We introduce the cipher and explain a ... Thank you for watching! If you got the help you need, please consider liking and subscribing! Thank you for the support towards ... The next talk is called Latin dances reloaded improved Cryptography and Network Security by Prof. D. Mukhopadhyay, Department of Computer Science and Engineering, IIT Kharagpur.
Léo Perrin and Aleksei Udovenko and Alex Biryukov, Crypto 2016. This video explains what cryptology, cryptography, and