Media Summary: A few years ago I created a set of presentations for a group of high school students on the fundamentals of Previous video Next video: ttps://youtu.be/tgWr-PS4UIU. In this session , let's see how the messages were encrypted before sending so that the enemies couldn't understand it.
Classic Cryptography Substitution Ciphers Part 2 - Detailed Analysis & Overview
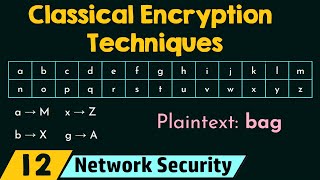
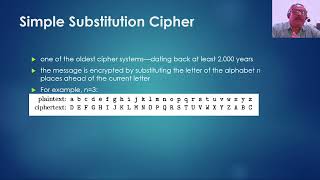
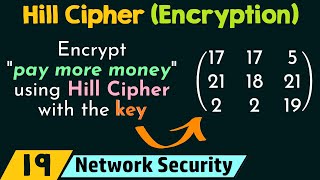
A few years ago I created a set of presentations for a group of high school students on the fundamentals of Previous video Next video: ttps://youtu.be/tgWr-PS4UIU. In this session , let's see how the messages were encrypted before sending so that the enemies couldn't understand it. Hello friends! Welcome to my channel. My name is Abhishek Sharma. In this video, i have explained various This video explain about the first technique of