Media Summary: Presented by: Jewel Marie C. Fabia MBA 1/3-12. In this episode of SIIMCast, we continue our mini-series exploring the Practical Imaging Informatics Resource Textbook (PIIRT) ... Upgrade your cybersecurity skills—enroll now: Course Introduction / Overview Ready to ...
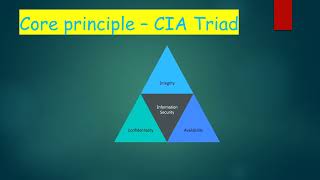
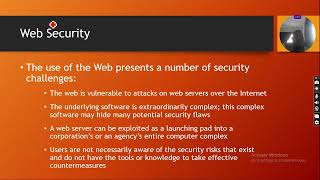
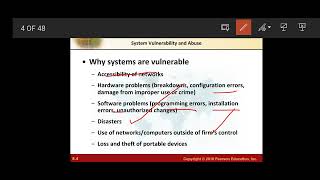
Chapter 8 Information Systems Security - Detailed Analysis & Overview
Presented by: Jewel Marie C. Fabia MBA 1/3-12. In this episode of SIIMCast, we continue our mini-series exploring the Practical Imaging Informatics Resource Textbook (PIIRT) ... Upgrade your cybersecurity skills—enroll now: Course Introduction / Overview Ready to ... Tech Today series is our meek effort to provide contents that are challenging, interactive and at the same time engaging the ... Mind Map for my assignment Created by InShot MIS CHAPTER 8 : Securing Information System
Cybersecurity Expert Masters Program ...