Media Summary: Making yourself the all-powerful "Root" super-user on a computer using a This is the fourth video in the Foundations of Exploitation series and in this video we'll explore how to gain This video provides a look at using the (ported) pattern_create and pattern_offset from metasploit to identify the layout of a ...
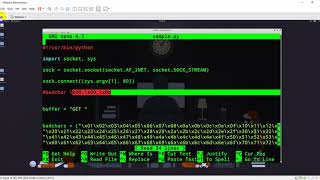
Buffer Overflows Rewriting Eip To Control Execution - Detailed Analysis & Overview
Making yourself the all-powerful "Root" super-user on a computer using a This is the fourth video in the Foundations of Exploitation series and in this video we'll explore how to gain This video provides a look at using the (ported) pattern_create and pattern_offset from metasploit to identify the layout of a ... Social Media ⭐ Discord: Twitter: Github: ... In this Week 12 assignment, we walk through a real-world style This is a series of three videos, which gives a quick start up on different exploitation and mitigation techniques for the
I created a script that automatically generates .c programs with intentional In this video, part 5 of the series, we'll talk about how to perform a "stack pivot". We've gained We write our first real exploit to get root access. Solving stack5 from exploit-exercises.com with a simple Ethical Hacking Beginners Tutorial 45 Understanding EIP, ESP Buffer Overflow 720p 30fps H264 192 Hi everyone! I hope you enjoyed this video. Please do consider subscribing so we can continue making awesome hacking ...