Media Summary: Making yourself the all-powerful "Root" super-user on a computer This tutorial goes over the basic technique of how to PS, jump into the HackTheBox Cyber Apocalypse CTF! Help the channel grow
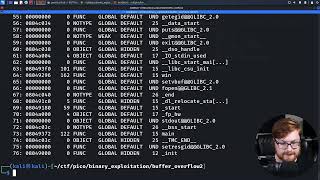
Buffer Overflow Attack Using Peda Debugger - Detailed Analysis & Overview
Making yourself the all-powerful "Root" super-user on a computer This tutorial goes over the basic technique of how to PS, jump into the HackTheBox Cyber Apocalypse CTF! Help the channel grow In this video, we'll continue our exploration of software exploitation by walking Buffer overflow attack using gdb-peda on 64-bit maching