Media Summary: Authors: Nilaksh Das, Haekyu Park, Zijie J. Wang, Fred Hohman, Robert Firstman, Emily Rogers, Duen Horng Chau VIS website: ... Machine learning is being used for lots of great things, from guiding autonomous cars to creating pictures of cats that don't actually ... ShapeShifter is the first targeted physical
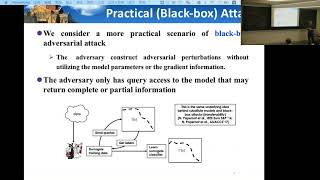
Bluff Interactively Deciphering Adversarial Attacks On Deep Neural Networks - Detailed Analysis & Overview
Authors: Nilaksh Das, Haekyu Park, Zijie J. Wang, Fred Hohman, Robert Firstman, Emily Rogers, Duen Horng Chau VIS website: ... Machine learning is being used for lots of great things, from guiding autonomous cars to creating pictures of cats that don't actually ... ShapeShifter is the first targeted physical Yuzhe You, Jarvis Tse, Jian Zhao. Panda or not Panda? In this video, we will understand the significance of Convolution This video was recorded as part of CIS 522 -
Approximate computing is known for its effectiveness in improvising the energy efficiency of