Media Summary: By: Matt Miller & Ken Johnson Over the past decade, Microsoft has added security features to the The Brave Browser is safer & much faster, based on Chrome. Earn crypto while your browse: By Corey Kallenberg, Xeno Kovah, and Samuel Scott Cornwell "The UEFI specification has more tightly coupled the bonds of the ...
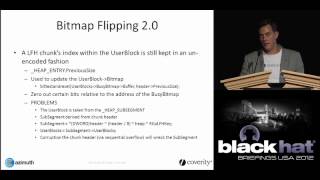
Blackhat 2012 Exploit Windows 8 - Detailed Analysis & Overview
By: Matt Miller & Ken Johnson Over the past decade, Microsoft has added security features to the The Brave Browser is safer & much faster, based on Chrome. Earn crypto while your browse: By Corey Kallenberg, Xeno Kovah, and Samuel Scott Cornwell "The UEFI specification has more tightly coupled the bonds of the ... By: Zhenhua 'Eric' Liu With the introduction of By: Cesar Cerrudo For some common local Kernel vulnerabilities there is no general, multi-version and reliable way to By: Yuriy Bulygin, Andrew Furtak & Oleksandr Bazhaniuk
By: Bill Sempf Security and privacy in mobile development has been a topic in the iOS and Android world for a few years now.