Media Summary: The Brave Browser is safer & much faster, based on Chrome. Earn crypto while your browse: By: Silvio Cesare Developers sometimes statically link libraries from other projects, maintain an internal copy of other software or ... Black Hat USA 2014 - Malware: Full System Emulation Achieving Successful Automated Dynamic Analysis
Blackhat 2012 Automated Malware Analysis - Detailed Analysis & Overview
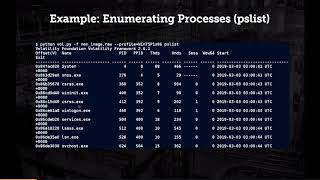
The Brave Browser is safer & much faster, based on Chrome. Earn crypto while your browse: By: Silvio Cesare Developers sometimes statically link libraries from other projects, maintain an internal copy of other software or ... Black Hat USA 2014 - Malware: Full System Emulation Achieving Successful Automated Dynamic Analysis By: Jeong Wook Oh We are seeing more and more Java vulnerabilities exploited in the wild. While it might surprise many users, ... This presentation mainly focuses on the practical concept of memory forensics and shows how to use memory forensics to detect, ... By: Abhishek Singh & Zheng Bu Diamonds are girl's best friend, prime numbers are mathematician's best friend and
Machine learning offers opportunities to improve By: Joshua Saxe Due to the exploding number of unique By: James Philput Network defenders face a wide variety of problems on a daily basis. Unfortunately, the biggest of those ... By: Zachary Hanif, Telvis Calhoun & Jason Trost Over the past 2.5 years Endgame received 20M samples of HITB2012KUL (OCT 10-11) REGISTRATION NOW OPEN