Media Summary: In this video I'm going to show what a hacker can do, using a man in the middle attack, if they are on the same network as you. In this video i have explained DNS poisoning attacks. How an attacker hack your personal details. Want to figure out why you ... Cyber Security Certification Notes & Cheat Sheets (2nd link) Cyber Security ...
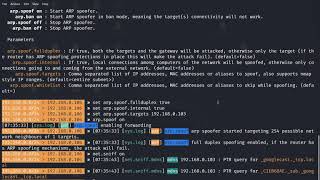
Bettercap Tutorial Part 2 - Detailed Analysis & Overview
In this video I'm going to show what a hacker can do, using a man in the middle attack, if they are on the same network as you. In this video i have explained DNS poisoning attacks. How an attacker hack your personal details. Want to figure out why you ... Cyber Security Certification Notes & Cheat Sheets (2nd link) Cyber Security ... Resources For EachTool We Will Use(Attacks/Exploits Are Not Listed): For Information Gathering: 1) Whatweb ... hook.js file: In this video you discover how to inject BeefHook JS with Welcome to RGSecurityTeam!* In this video, we demonstrate how to capture a WiFi handshake using *
Membership // Want to learn all about cyber-security and become an ethical hacker? Join this channel now to gain access into ... ARP and DNS spoofing are often discussed in theory — but seeing them happen in a live lab is what makes them truly click. This channel is all about ethical hacking in telugu . please find required links below. ... This is a reupload of a video - Youtube doesnt seem to like my descriptions/titles/videocontent so i edited all of them and made ... This video is a beginner-friendly introduction to