Media Summary: Yay hello everybody um welcome back day two of In this video wallthrough, we covered the second solution walkthrough of Cyberry Vulnhub lab where we demonstrated We'll be covering the very basics required to understand what makes a Linux executable run from the perspective of someone ...
B01lers Ctf Bootcamp Binary Exploitation 1 - Detailed Analysis & Overview
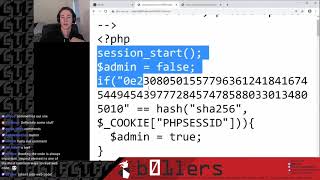
Yay hello everybody um welcome back day two of In this video wallthrough, we covered the second solution walkthrough of Cyberry Vulnhub lab where we demonstrated We'll be covering the very basics required to understand what makes a Linux executable run from the perspective of someone ... Covering crackme0x00a, crackme0x00b, crackme0x01, crackme0x02 Modern