Media Summary: Authentication Based Access Control Issues Hey everyone, In this video, we are going to see various role- Try Clerk: *Become a web developer* with my *FREE Web Development Roadmap* - _260+ videos, ...
Authentication Based Access Control Issues - Detailed Analysis & Overview
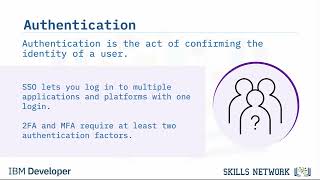
Authentication Based Access Control Issues Hey everyone, In this video, we are going to see various role- Try Clerk: *Become a web developer* with my *FREE Web Development Roadmap* - _260+ videos, ... Welcome back to behardikjoshi! We all use This video is a beginner-friendly guide to the concepts of In this video, Microsoft Entra ID Program Manager Stuart Kwan explains the basic concepts and fundamental workings of ...
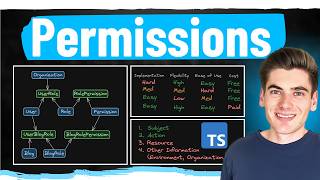
As AI agents transform enterprise software, securing them with robust identity and Sections 0:00 Introduction 0:52 What is Authorization 1:47 Authorization Models 2:54 RBAC: Role- In this tutorial, you'll learn how to implement Role- CyberPlatter Discord Channel: Website: Security Analyst and Engineer ...