Media Summary: Disclaimer: Hacking without permission is illegal. This channel is for educational purposes only.* Discover the captivating realm of network scanning and remote access in this educational YouTube video. Join us as we explore ... Hi there, In this video we continue the Active Directory Exploitation series. This episode in particular focuses on the different ...
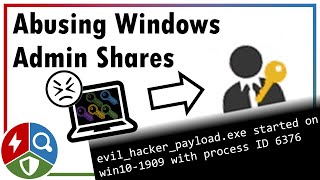
Attack Smb Psexec - Detailed Analysis & Overview
Disclaimer: Hacking without permission is illegal. This channel is for educational purposes only.* Discover the captivating realm of network scanning and remote access in this educational YouTube video. Join us as we explore ... Hi there, In this video we continue the Active Directory Exploitation series. This episode in particular focuses on the different ... Commands Used (in the order that they appear in the video): 1. ifconfig 2. nmap -sV -sC 10.10.50.1 3. service postgresql start ... In this episode, we're going to look at a variety of methods you can use to determine whether or not a system was the recipient of a ... In this video, we dive into two powerful methods for obtaining shell access after capturing hashes through
Are you looking for an easy way to manage your In this video, I will be exploring the process of performing lateral movement on A quick demo of new tool I wrote. It is yet another This video for educational purposes dont use for bad. 00:00:00:36 - Entry --------------------------------- 00:37:01:17 Q1-Q2 --------------------------------- 01:18:02:05 Q3-Q4 ...