Media Summary: Keeper Security offers a privileged access management solution to deliver enterprise grade protection all in ... Learn the tools and techniques that can help you identify and How did 4chan get hacked? Turns out it was a
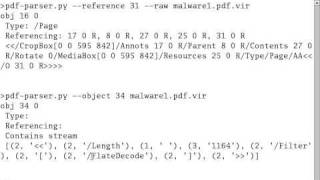
Analyzing A Malicious Pdf File - Detailed Analysis & Overview
Keeper Security offers a privileged access management solution to deliver enterprise grade protection all in ... Learn the tools and techniques that can help you identify and How did 4chan get hacked? Turns out it was a In this presentation, Filipi Pires will introduce attendees to the basics of Download the pcap here and follow along: https:// Read our blog post about Attachments in Phishing
Hello again to another blue team CTF walkthrough now for a bit of