Media Summary: Welcome to 4DeepLearn! Aaj ke video mein hum seekhenge ** To help explain how attackers reverse engineer device firmware, this walkthrough takes a piece of firmware from a by Christopher Kruegel & Yan Shoshitaishvili Over the last few years, as the world has moved closer to realizing the idea of the ...
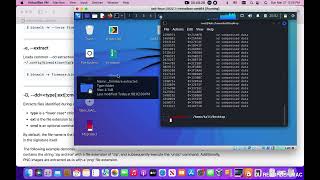
Analyzing A Binary File Using Binwalk - Detailed Analysis & Overview
Welcome to 4DeepLearn! Aaj ke video mein hum seekhenge ** To help explain how attackers reverse engineer device firmware, this walkthrough takes a piece of firmware from a by Christopher Kruegel & Yan Shoshitaishvili Over the last few years, as the world has moved closer to realizing the idea of the ... Linux Command Line tutorial for forensics - 03 - looking at This video explains how to perform firmware The Book excerpts are from a book on practical
Black Hat - USA - 2015 Hacking conference , , , , , . User interaction is required to exploit this vulnerability in that the target must open the malicious