Media Summary: In case you didn't have time for our 2-minutes introduction to the topic ( :) More information at: ... Read our blog post about Attachments in Phishing In this workshop (2 hours), I explain how to use the tools (oledump, emldump, YARA rules, …) I developed to
Analysis Malicious Excel File - Detailed Analysis & Overview
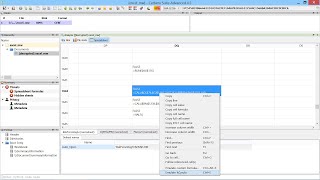
In case you didn't have time for our 2-minutes introduction to the topic ( :) More information at: ... Read our blog post about Attachments in Phishing In this workshop (2 hours), I explain how to use the tools (oledump, emldump, YARA rules, …) I developed to Integrate ANY.RUN solutions into your company: ... In this eye-opening educational video, we uncover the hidden dangers of We have uploaded a version of the same video with a better audio here: Using Cerbero Suite to ...
If you would like to support the channel and I, check out Kite! Kite is a coding assistant that helps you code faster, on any IDE offer ... In this video we introduce the formula view, which is extremely useful when analyzing obfuscated Analysis of Malicious Excel Document - Process Inspections