Media Summary: Justin works through the process of finding the Affine Cipher Encryption Technique with Example In this video i have explained how to solve
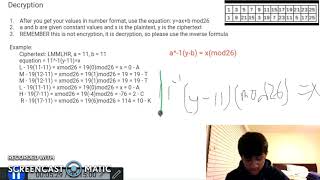
Affine Cipher Decryption Known Key - Detailed Analysis & Overview
Justin works through the process of finding the Affine Cipher Encryption Technique with Example In this video i have explained how to solve In this video, We are discussing about the information related to We use a brute-force attack to hack a message encrypted with the Cryptanalysis of Monoalphabetic cipher such as