Media Summary: DEF CON 25 - JoSh Pitts - Teaching Old Shellcode New Tricks ... sure that we can google the syntax if you forgot something or yeah the We write our first real exploit to get root access. Solving stack5 from exploit-exercises.com with a simple Buffer Overflow and ...
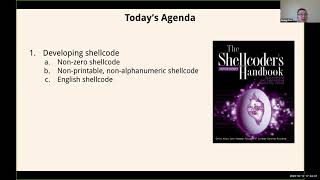
Advanced Shellcode With Caffix - Detailed Analysis & Overview
DEF CON 25 - JoSh Pitts - Teaching Old Shellcode New Tricks ... sure that we can google the syntax if you forgot something or yeah the We write our first real exploit to get root access. Solving stack5 from exploit-exercises.com with a simple Buffer Overflow and ... This playlist has a list of free videos from the course "Exploit Development for Linux (x86)". If you are interested in viewing the full ... After spending last year analyzing APT attacks, I plan to investigate how A= This is the second video continuing through the freely available Corelan Tutorials! More specifically, in this video we will be ...
Reverse Engineering: Carving Shellcode from Memory with x64dbg + scdbg, Shellcode Analysis In this video, we analyze a Cobalt Strike Loader — a powerful component often used in post-exploitation frameworks — and dive ... Kickstart your career in Ethical Hacking with these courses Ultimate Ethical Hacking and Penetration Testing (UEH): ... In this presentation, we will go over the basics of writing
![[Advanced] Shellcode with Caffix](https://i.ytimg.com/vi/xgzJXkSM7UQ/mqdefault.jpg)