Media Summary: 48 Implementing DoS Attack with SYN Flooding This is something I did over a month ago for fun. I've always wondered how to perform a cyber Attackers are taking advantage of weaknesses in the DNS protocol in order to launch a high bandwidth sophisticated
48 Implementing Dos Attack With Syn Flooding - Detailed Analysis & Overview
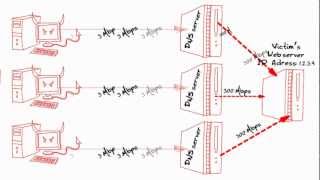
48 Implementing DoS Attack with SYN Flooding This is something I did over a month ago for fun. I've always wondered how to perform a cyber Attackers are taking advantage of weaknesses in the DNS protocol in order to launch a high bandwidth sophisticated Watch this Radware Minute episode with Radware's Eva Abergel to learn what is a TCP This is the quickest and most painful way to cause damage on the internet, by causing slow responses and major outages. In this lecture we will be looking at 1. What is a
In this video, we explore everything about DoS and Watch this Radware Minute episode with Radware's Eva Abergel to learn what is a Ransom IT Trainers Introduction: Junior Network Administrator Program Junior Network Administrator Program Information We are ... In this video, we demonstrate how to perform and analyze a