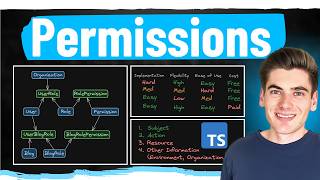
Media Summary: Get the threat intelligence guide → Learn about the technology → Exploring the ... Role-based access control (RBAC) is an essential method for managing permissions in cloud systems. In this video, Varun sir ... 33 Role Based and Rule Based Access Control RBAC
33 Role Based And Rule Based Access Control Rbac - Detailed Analysis & Overview
Get the threat intelligence guide → Learn about the technology → Exploring the ... Role-based access control (RBAC) is an essential method for managing permissions in cloud systems. In this video, Varun sir ... 33 Role Based and Rule Based Access Control RBAC Hey everyone, In this video, we are going to see various CyberPlatter Discord Channel: Website: Security Analyst and Engineer ... This video is part of the Udacity course "Intro to Information Security". Watch the full course at ...
Welcome to the 18th video in the series! In this video, we dive into the world of Azure Want to Become a Data Engineer? Then Azure Data Factory is a Must! In this video, you will learn the complete details about ... CBT Nuggets trainer Trevor Sullivan covers creating new users in Azure and assigning them permissions with