Media Summary: I'm ProwlSec, a Cybersecurity Researcher with a deep passion for all things tech. My journey is all about becoming a ... Here's a **YouTube video description (and optional script)** for a video titled: **" Bug Type - Improper Authentication – Generic CWE-287 Steps To Reproduce: 1. First we click on login and then click to forget ...
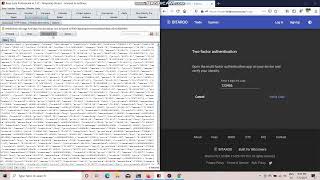
2fa Bypass Vulnerability Poc - Detailed Analysis & Overview
I'm ProwlSec, a Cybersecurity Researcher with a deep passion for all things tech. My journey is all about becoming a ... Here's a **YouTube video description (and optional script)** for a video titled: **" Bug Type - Improper Authentication – Generic CWE-287 Steps To Reproduce: 1. First we click on login and then click to forget ... Disclaimer: Hacking without permission is illegal. This channel is strictly educational for learning about cyber-security in the areas ... In this video, we will learn about 5 different ways to hunt for Authentication Telegram link: bug bounty, bug bounty hunting, bug bounty
In this video, we cover Lab in the Authentication module of the Web Security Academy. This lab's 2FABypass This video demonstrates a real-world Join this channel to get access to the perks: References: ...