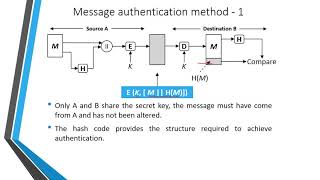
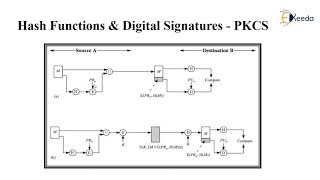
Media Summary: MIT 6.046J Design and Analysis of Algorithms, Spring 2015 View the complete course: Instructor: ... Three types of Authentications 1. Message In this video you will understand all about what is
21 Cryptography Hash Functions - Detailed Analysis & Overview
MIT 6.046J Design and Analysis of Algorithms, Spring 2015 View the complete course: Instructor: ... Three types of Authentications 1. Message In this video you will understand all about what is This video will help you understand the SAS user interface and help you understand Almost every piece of technology we use today has some kind of embedded firmware. Rogue firmware, however, can leak data ...