Media Summary: In this video, I have solved the "Using the This is the second video in my Path towards my GXPN. The GXPN is the SANS 660: Advance pentesting and This video is part of the computer/information/cyber security and ethical hacking lecture series; by Z. Cliffe Schreuders at Leeds ...
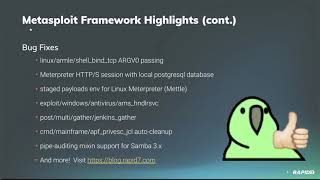
04 Developing Metasploit Module - Detailed Analysis & Overview
In this video, I have solved the "Using the This is the second video in my Path towards my GXPN. The GXPN is the SANS 660: Advance pentesting and This video is part of the computer/information/cyber security and ethical hacking lecture series; by Z. Cliffe Schreuders at Leeds ... Based on ManageEngine Exchange Reporter Plus Unauthenticated Remote Code Execution Oracle Virtualbox installation link - In this session we will take a look at the ... Want to go beyond basics? Get my Network Scanning For Hacker Beginner to Pro (NO BS): ...
Hack in the Box - 2006 - Malaysia Hacking conference , , , , , . Ethical Hacking with Metasploitable2 (Part 2) Welcome to Part 2 of our Ethical Hacking with Metasploitable2 series! Hey, guys HackerSploit here, back again with another video. In this video, we will be continuing the Complete