Media Summary: (2 of 4) Work-through tutorial on creating a I created this video to summarize the the first few chapters of the open source book Crypto101, which I have linked below. (3 of 4) Work-through tutorial on creating a
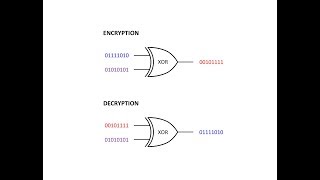
02 Xor Cipher Characters And Binary - Detailed Analysis & Overview
(2 of 4) Work-through tutorial on creating a I created this video to summarize the the first few chapters of the open source book Crypto101, which I have linked below. (3 of 4) Work-through tutorial on creating a (1 of 4) Work-through tutorial on creating a This is the fourth in a series about cryptography; an extremely important aspect of computer science and cyber security. It covers ... 00:00 - Intro 00:35 - Describing frequency analysis 01:10 - Downloading a book from Project Gutenberg and counting
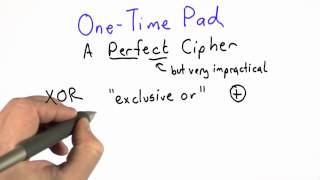
Created using PowToon -- Free sign up at -- Create animated videos and animated ... This video is part of an online course, Applied Cryptography. Check out the course here: