Media Summary: Hepinize merhabalar ben Volkan Özdemir. Bu videoda Resources For EachTool We Will Use(Attacks/Exploits Are Not Listed): For Information Gathering: 1) Whatweb ... Hello hackers, in this video we are going to solve
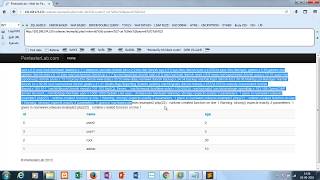
Web Pentesterlab Command Injection - Detailed Analysis & Overview
Hepinize merhabalar ben Volkan Özdemir. Bu videoda Resources For EachTool We Will Use(Attacks/Exploits Are Not Listed): For Information Gathering: 1) Whatweb ... Hello hackers, in this video we are going to solve Welcome to GURUKULA! In this tutorial, we delve into the critical topic of ** For my MS Cybersecurity at St. Bonaventure University, a complete walk-through of Each of our labs comes with a comprehensive manual to guide you. In the example below, you will learn to perform
Membership // Want to learn all about cyber-security and become an ethical hacker? Join this channel now to gain access into ...