Media Summary: This is something I did over a month ago for fun. I've always wondered how to perform a cyber Watch this Radware Minute episode with Radware's Eva Abergel to learn what is a TCP 11.6.8 Analyze a SYN Flood Attack : TestOut
Syn Flood Attack - Detailed Analysis & Overview
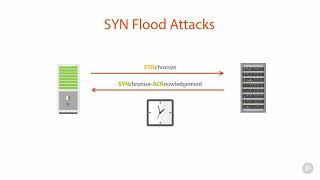
This is something I did over a month ago for fun. I've always wondered how to perform a cyber Watch this Radware Minute episode with Radware's Eva Abergel to learn what is a TCP 11.6.8 Analyze a SYN Flood Attack : TestOut This chalk talk video, which is part of a broader series on Denial-of-Service What is IP Spoofing - To the Point Explanation in URDU/HINDI NETWORK ... In this video, we demonstrate how to perform and analyze a
This video explains TCP 3-way handshake and In this video we will learn about how to detect ... video, we look at what SYN cookies are and how they can be used for TCP authentication to protect against Welcome to the World of Cybersecurity! In this video, we dive into the Start learning cybersecurity with CBT Nuggets. In this video, Keith Barker covers what TCP In this lecture we will be looking at 1. What is a DOS