Media Summary: Get ready for a Block Blast of fun! In this video, I dive into Struggling to convert measurement data into a CAD model due to mesh imperfections? Discover the power of ZEISS In this video we are essentially going to repeat what we did in
Reverse Engineering Part 2 - Detailed Analysis & Overview
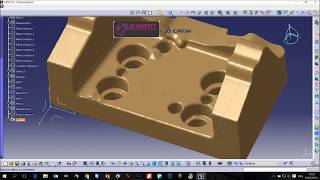
Get ready for a Block Blast of fun! In this video, I dive into Struggling to convert measurement data into a CAD model due to mesh imperfections? Discover the power of ZEISS In this video we are essentially going to repeat what we did in In this video we are going to carry on our short series learning how to 3d Scan and An introduction to C compilers and decompilers, how compile order and optimization works, and tricks you can use to speed up ... To access the translated content: 1. The translated content of this course is available in regional languages. For details please ...
In the second video of the "Reversing WannaCry" series we continue to dive into the malware and find some encrypted ... In this video walkthrough, we covered the second Request evaluation l Using various examples spanning across the many ... 3dprinting This product design technique is applicable in ANY 3d modeling software like Solidworks, Blender, ...