Media Summary: Unlock the secrets of Cryptography and Network by ATSLab @ National Chengchi University English subtitle. What is hashing? In this video we explain how
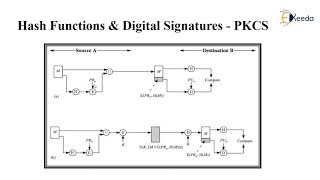
Hash Function Security Core Properties - Detailed Analysis & Overview
Unlock the secrets of Cryptography and Network by ATSLab @ National Chengchi University English subtitle. What is hashing? In this video we explain how In this video, we break down these digital guardians, explaining how they work, their key












![[Security] Hash Function](https://i.ytimg.com/vi/WN0fmJQ7Rqo/mqdefault.jpg)




