Media Summary: Want to support this channel without having to splash out?⚠⛔ Simply use the links below and XL Pro Tech will receive some ... If you don't know about them, they'll be used against you. With the upcoming rise of AI agents that will be working on our behalf, ... On June 27, 2017, almost all of Ukraine was paralyzed by NotPetya: a piece of malware designed with a single purpose - to ...
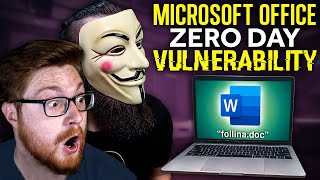
Exploit Doc - Detailed Analysis & Overview
Want to support this channel without having to splash out?⚠⛔ Simply use the links below and XL Pro Tech will receive some ... If you don't know about them, they'll be used against you. With the upcoming rise of AI agents that will be working on our behalf, ... On June 27, 2017, almost all of Ukraine was paralyzed by NotPetya: a piece of malware designed with a single purpose - to ... How did 4chan get hacked? Turns out it was a malware postscript in a pdf upload box that got all the admins exposed and ended ... Want to become a HACKER? ITProTV has you covered: (30% off FOREVER) *affiliate link In this video ... Hello world and welcome to HaXeZ, in this post I'm going to be explaining how you can hack anyone with a Microsoft Office ...
Disclaimer: This video is for educational purposes only. In this video, we explore what a FUD Crypter , PDF Disclaimer: The content presented in this video is intended for educational and informational purposes only. The techniques, tools ... Welcome to our video introducing Olymposs, a powerful FUD (Fully Undetectable) crypter designed to secure and protect your ... In this series, I will show you how I developed my first real world windows 01:05 - Start of nmap 04:00 - Using ffuf to find the panel subdomain, which shows pterodactyl.htb 06:30 - Discovering the version ... This tool help you attach an execute file (.exe) into Microsoft Word (.