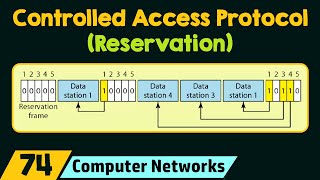
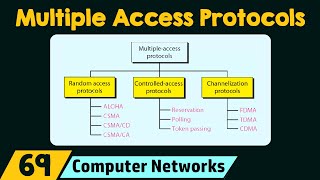
Media Summary: 00:00:00-Reservation 00:03:28-Pooling 00:09:36-Token Passing # Please message us on WhatsApp: KnowledgeGate Website: Gate Smashers Shorts: Watch quick concepts & short videos here: Subscribe ...
Controlled Access Protocols - Detailed Analysis & Overview
00:00:00-Reservation 00:03:28-Pooling 00:09:36-Token Passing # Please message us on WhatsApp: KnowledgeGate Website: Gate Smashers Shorts: Watch quick concepts & short videos here: Subscribe ... Download Notes of All Subjects from the Website: Or ... ... CSMA) 19:45 - CSMA/CD protocol 22:01 - CSMA/CA protocol 23:37 - CyberPlatter Discord Channel: Website: Security Analyst and Engineer ...
Computer Network (KCS603), According to AKTU Syllabus, complete syllabus (full course) covered