Media Summary: in this one i'll be showing you guys how to perform a stack This tutorial goes over the basic technique of how to The eighth and final video in a series covering x86 stack
Buffer Overflow Remote Exploit - Detailed Analysis & Overview
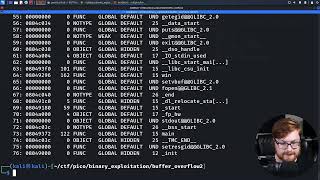
in this one i'll be showing you guys how to perform a stack This tutorial goes over the basic technique of how to The eighth and final video in a series covering x86 stack Making yourself the all-powerful "Root" super-user on a computer using a Are you a security researcher or reverse engineer? For 50% off IDA Products use promo code BILLY50, ... PS, jump into the HackTheBox Cyber Apocalypse CTF! Help the channel grow with a ...
This video will teach take teach you what we mean by This lecture is part of my undergraduate security course at the University of Cambridge. 00:00 Challenges and intro 01:40 What is ...